What is Passwordless Authentication?
Creating, remembering, and periodically changing passwords is no fun. Nowadays, passwords are an outdated and less secure method of authentication. Currently, a password alone is not enough security and often coexists with another authentication method. In addition to entering a password consisting of lowercase and uppercase letters, numbers, and symbols, the login form will ask you for a code that will appear on your smartphone. Although more secure, MFA can be annoying when it disrupts your workflow. It seems that security does not go hand in hand with convenience. But does it really? This article will present the concept of Passwordless Authentication.
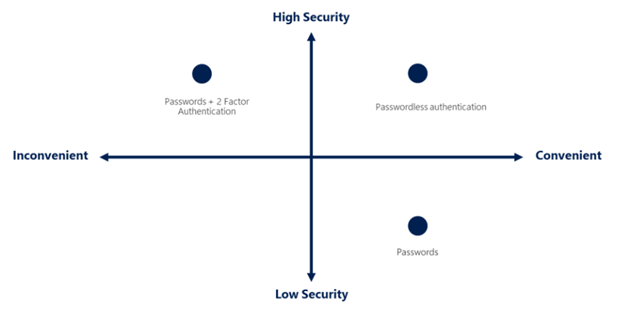
Passwordless authentication combines convenience with security. Not using a password minimizes the possibility of its leakage. There is also no need to enter a dozen or so characters to access your data. You just need to use an application, hardware key, or another convenient method.
Passwordless Authentication – a method of authentication that involves replacing a password with something you have, something you know, or who you are. Among other things, you can use the following to log in:
• Biometrics – fingerprint, face scan, iris scan
• Hardware keys – FIDO2
• Phone app – Microsoft Authenticator, Google Authenticator
• SMS
Configuring Passwordless Authentication on the example of Azure AD.
Microsoft provides the option of passwordless login for Azure Active Directory users. At present, noteworthy available login methods are:
• Windows Hello for Business
• FIDO2 hardware key
• Microsoft Authenticator app
• SMS
• Phone call
However, before a user can make the login process easier, proper configuration is necessary.
First, log in to https://portal.azure.com as a Global Administrator. Open Azure Active Directory and navigate to Manage -> Security -> Authentication methods -> Policies.
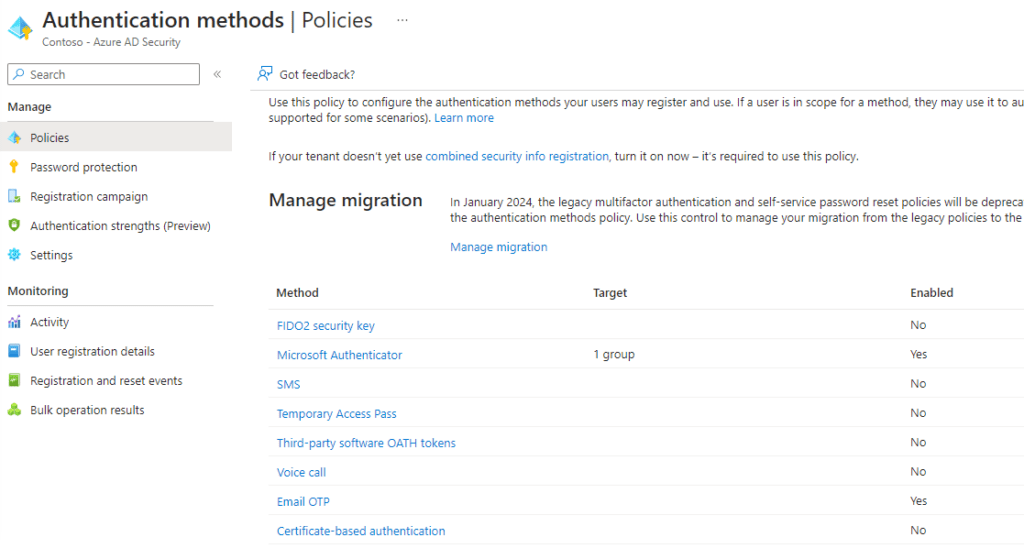
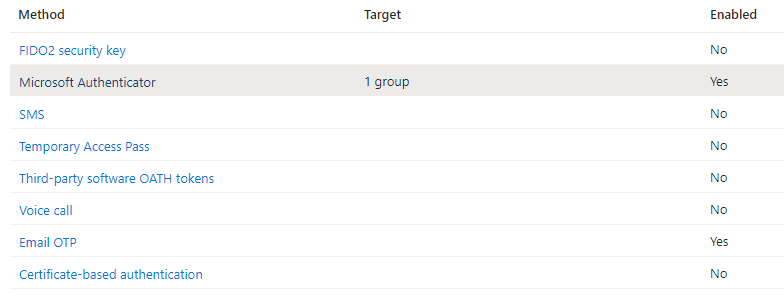
Available authentication methods will appear. Select the desired solution (in this example, I will use the Microsoft Authenticator application).
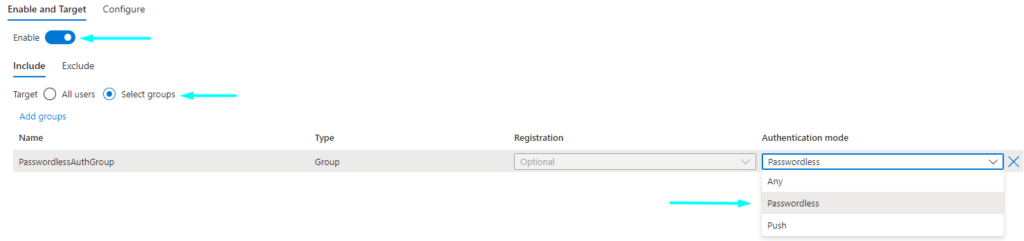
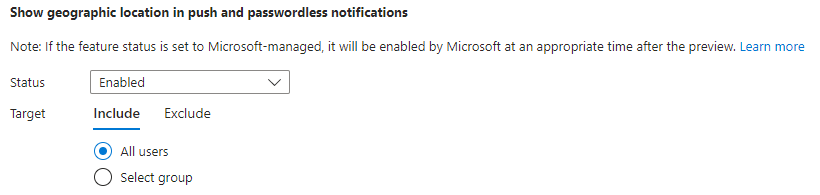
The “Enable” switch activates the authentication method. In the “Include / Exclude” fields, select who the policy will apply to. “Authentication mode” – here the Passwordless option should be selected. In the “Configure” tab, there is an option to customize the details of the Microsoft Authenticator application notification (for example, displaying the location from which the login was made).
After completing the configuration, save it with the “Save” button.
Configuring Passwordless Authentication in the Authenticator app
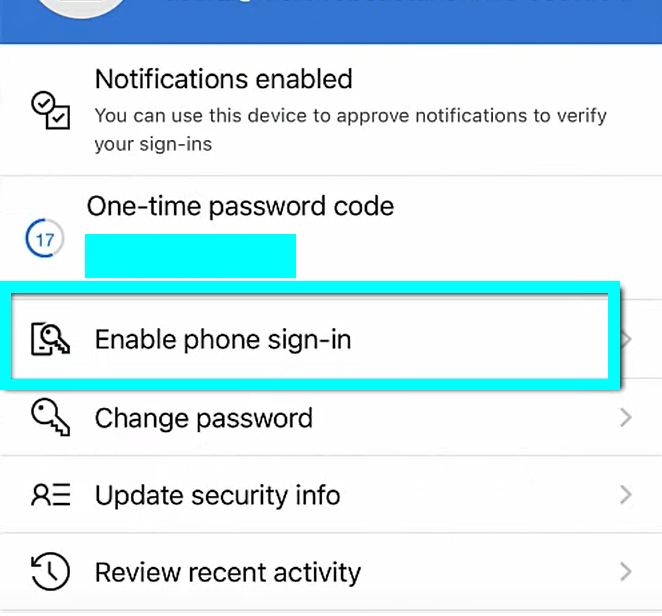
In the case of our configuration, to use passwordless authentication, it is required to install and log into the Microsoft Authenticator app with a work account. It is also necessary to enable the option to log in with your phone in the application settings:
Passwordless Authentication in practice
Successfully configured authentication looks like this:
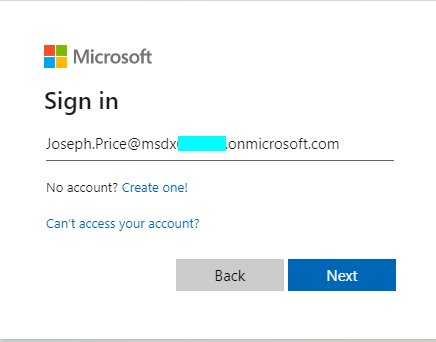
- The user logs in to the office.com portal.
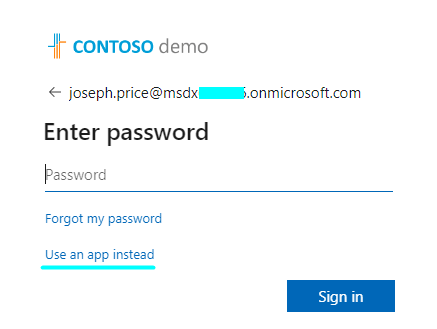
2. Asked for a password, choose the option to log in with the app.
3. The number is displayed.
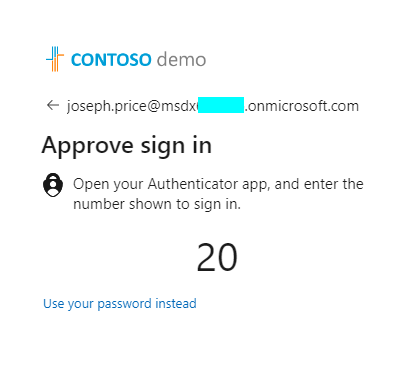
4. The Authenticator app displays a notification in which the above number must be entered. After correctly completing the form, the user is logged in.
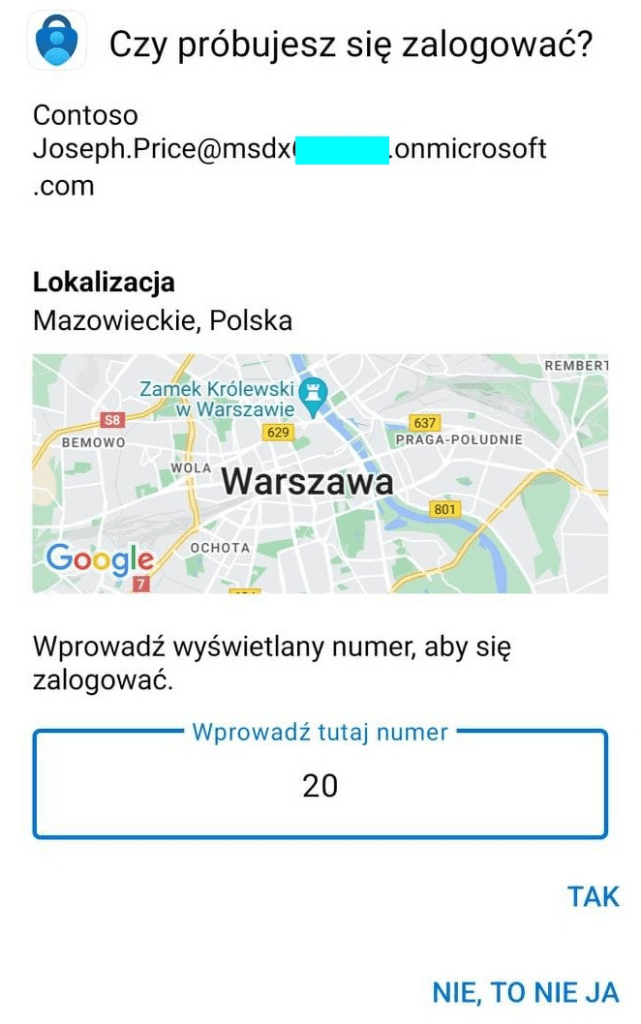
According to the earlier configuration, the notification shows the login location.
Summary
Passwordless Authentication is a much more convenient and secure solution than passwords, although at the moment it is a coexisting method with password-based login. Even though the user doesn’t have to use a password to log in, it doesn’t mean that passwords don’t exist. It is very likely that in the future we will completely get rid of passwords in favor of other authentication methods.


