AD PIM
Azure AD PIM allows for effective and secure management of access to privileged roles in the Azure cloud. This solution reduces the possibility of a hacker or fraudster obtaining permissions.
The functionalities of Azure AD PIM include:
• “Just-in-time” access to Azure resources
• Allocation of access to privileged roles within a specified time window
• Approval required to activate access
• Multi-factor authentication enforced
• Justification of privileged access
• Notifications of privileged role activation
• Access reviews of roles
• History of activations and accesses
• Safeguard against the loss of access to the Global Administrator and Privileged Role Administrator accounts
Why Privileged Identity Management?
In today’s dynamic IT environment, data is a crucial asset for every organization. Protecting access to sensitive data should be a priority. As the number of users and permissions increases, managing access and privileged roles becomes more complex. In particular, administrative and privileged accounts should be protected as they have the ability to access large amounts of sensitive data. The identity of an administrator and high-level permissions are also a target for unauthorized individuals who want to harm your organization. Therefore, it is necessary to secure your environment in accordance with the “The principle of least privilege.”
Access Management in PIM
Access to PIM is granted for:
- Users
- Groups
- SPN (service principals)
Depending on how granular the permissions should be, PIM allows for the specification of “Scope Tags” in addition to roles:
- Azure AD Roles
- Directory
- Administrative Unit
- Application
- Service Principal
- Azure AD Groups
- Owner
- Member
- Azure resources
- Management Group
- Subscription
- Resource Group
- Resource
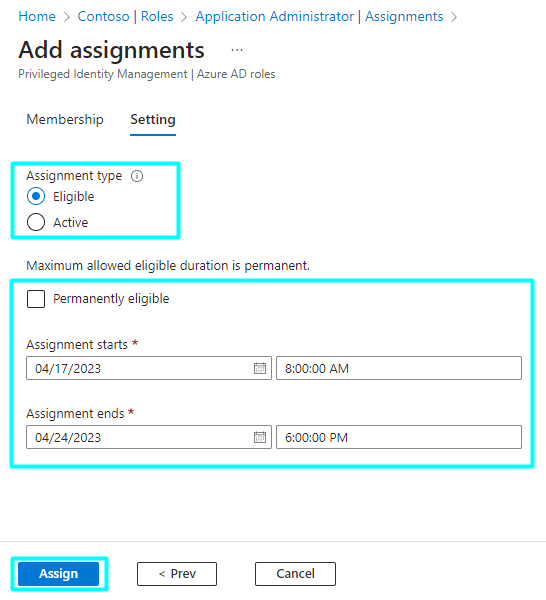
Types of assignments:
• Eligible – the user must activate their permissions before accessing. Activation may require MFA, providing business justification, or requesting approval from authorized users.
• Active – activation is not required. The role is active all the time.
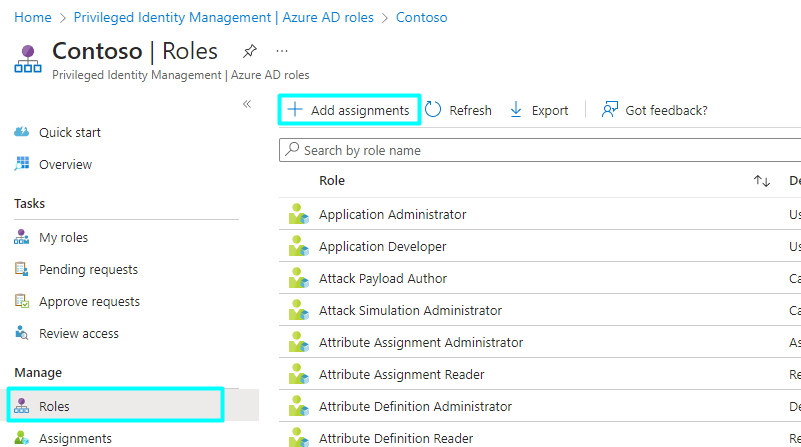
Role assignments can also be time-limited. Settings allow for the definition of a time interval for role assignment (start and end date of assignment). Let’s follow the process of assigning the “Application Administrator” role to one of the IT department employees for the next week. Their task is to make changes to the organization’s applications. You can perform a new role assignment in PIM > Azure AD roles > Roles using the “Add assignments” button.
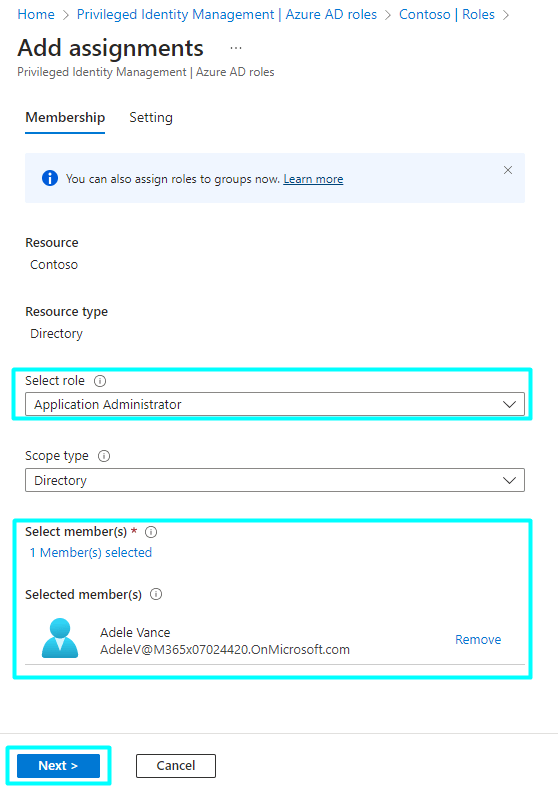
In the “Select role” window, we select the “Application Administrator” role. In “Scope tags,” we leave the option as “Directory” because we do not want to limit administrative access to specific applications.
The “Next” button will take us to the assignment settings. We choose the Eligible Assignment type (we want the user to activate the role before using it) and the start and end dates – in this case, it will be a week. Click “Assign”.
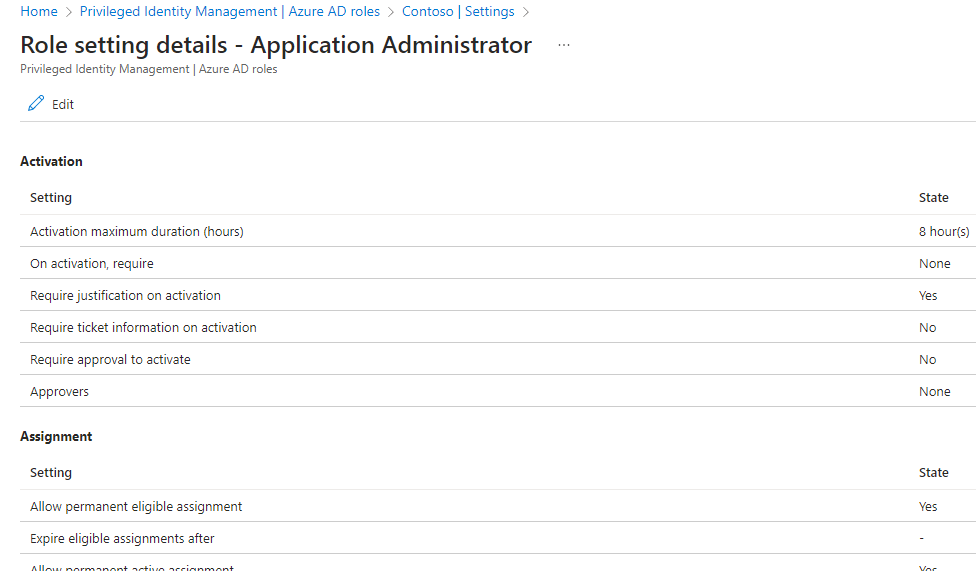
In the PIM > Azure AD Roles > Settings tab, we customize the requirements, alerts, and assignment details for a given role.
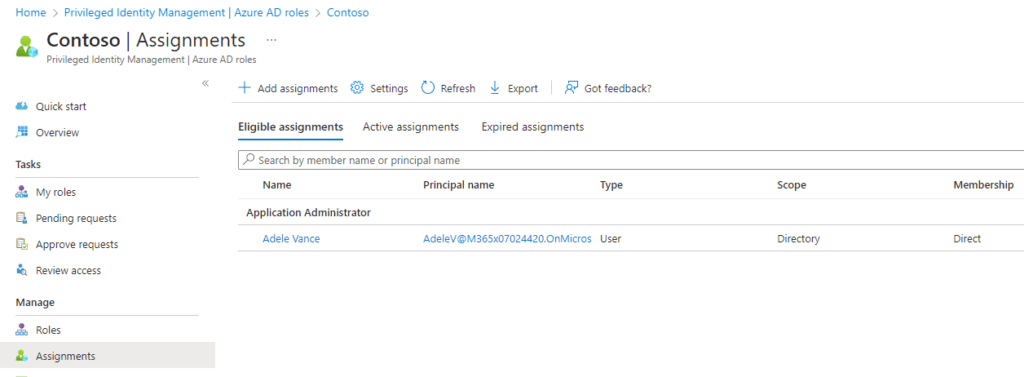
Assignments can be viewed and managed in the “Assignments” tab.
Access reviews
“Access Reviews” is a tool that allows for periodic reviews to identify and remove unnecessary permissions, minimizing the risk of unauthorized access. The results of the reviews are recorded and documented in Azure PIM, allowing for auditing and monitoring of permission changes. If inappropriate permissions are identified, administrators can quickly take corrective actions such as removing or restricting a user’s permissions. The “Access Reviews” option is only available for Azure AD roles and Azure resources and is currently not available for Azure AD groups.
Let’s create an example access review for the “Application Administrator” role (PIM > Azure AD Roles > Access Reviews > New).
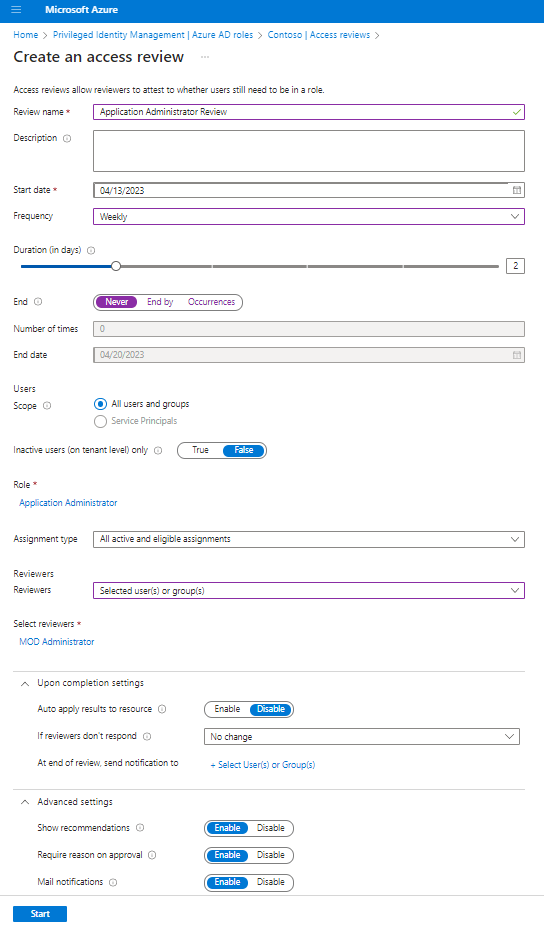
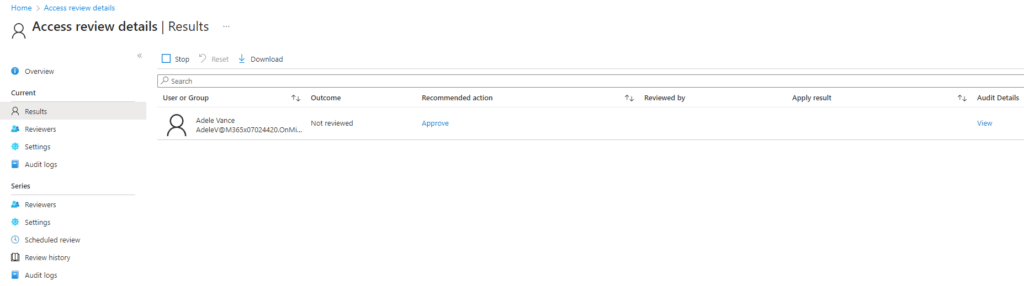
Reviews can be customized to suit specific needs. In this case, a two-day review that takes place weekly has been configured. It applies to all users and groups and all types of assignments. The result of the review looks as follows:
Summary
Azure Privileged Identity Management (PIM) is an important tool offered by the Microsoft Azure platform. It enables effective management of roles and permissions, while minimizing the risk of identity takeover attacks. With PIM, your permissions will be organized and transparent. It is definitely a solution worth trying!