2-Hours Briefing
Microsoft Teams Deployment
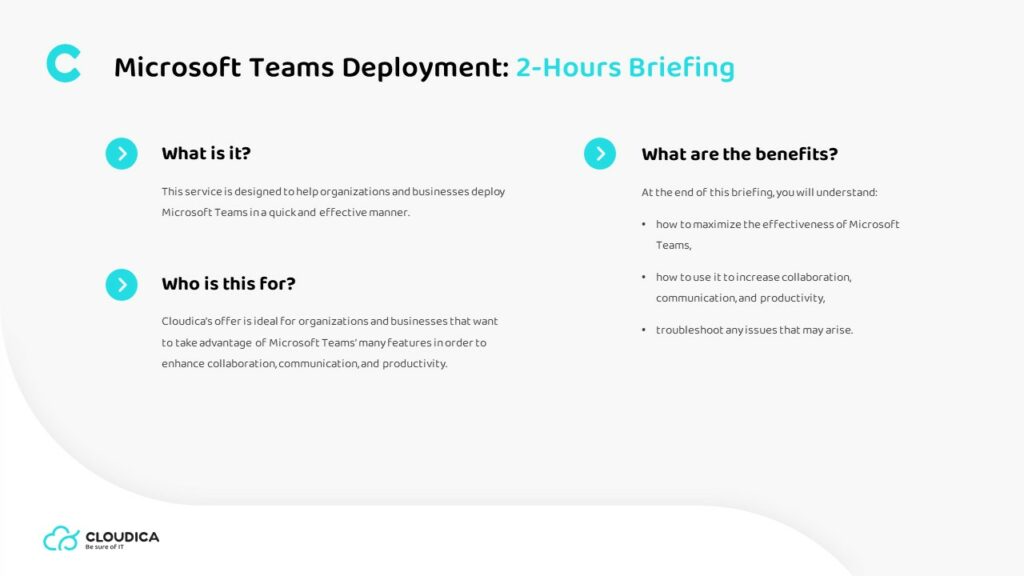
What is it?
This service is designed to help organizations and businesses deploy Microsoft Teams in a quick and effective manner.
What is for?
Cloudica’s offer is ideal for organizations and businesses that want to take advantage of Microsoft Teams’ many features in order to enhance collaboration, communication, and productivity.
What are the benefits?
At the end of this briefing, you will understand:
• how to maximize the effectiveness of Microsoft Teams,
• how to use it to increase collaboration, communication, and productivity,
• troubleshoot any issues that may arise.
Outcomes of this
The outcomes of the briefing include:
• an understanding of how Microsoft Teams can benefit your specific business needs
• how you can make the most of its features
• hands-on experience with the tools
Steps and agenda
• A discussion of the needs of the business
• An overview of the Teams deployment process,
• A discussion of best practices for Teams deployment
• Q&A session
Most popular offerings
Contact
Ready to meet the only technology partner you'll ever need?