5-Weeks Implementation
Migration to Microsoft 365
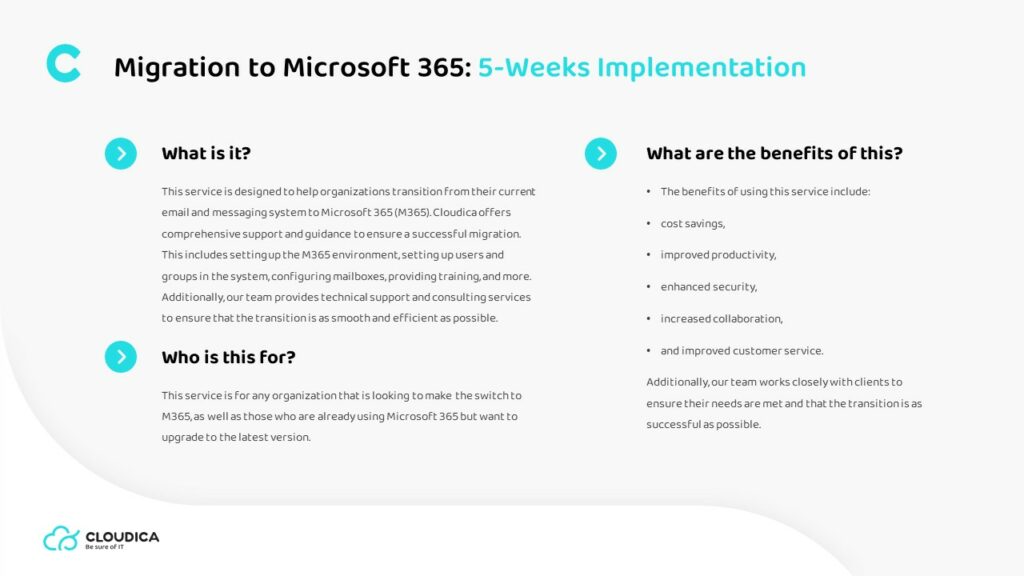
What is it?
This service is designed to help organizations transition from their current email and messaging system to Microsoft 365 (M365). Cloudica offers comprehensive support and guidance to ensure a successful migration. This includes setting up the M365 environment, setting up users and groups in the system, configuring mailboxes, providing training, and more. Additionally, our team provides technical support and consulting services to ensure that the transition is as smooth and efficient as possible.
What is for?
This service is for any organization that is looking to make the switch to M365, as well as those who are already using Microsoft 365 but want to upgrade to the latest version.
What are the benefits?
The benefits of using this service include:
• cost savings,
• improved productivity,
• enhanced security,
• increased collaboration,
• and improved customer service.
Additionally, our team works closely with clients to ensure their needs are met and that the transition is as successful as possible.
Outcomes of this
Cloudica offers comprehensive support and guidance to ensure a successful migration. This includes:
• setting up the M365 environment,
• setting up users and groups in the system,
• configuring mailboxes,
• providing training,
• at the end of the 5-week process, clients can be sure that their system is secure, reliable, and up to date with the latest version of Microsoft 365.
Steps and agenda
Week 1: Establish initial IT infrastructure
• Meet with client to discuss project and assess current IT infrastructure
• Assess current IT requirements and develop migration plan
• Determine necessary hardware and software requirements
• Set up initial IT infrastructure
Week 2: Migrate existing data and applications
• Begin transitioning existing data and applications to the new platform
• Identify and resolve any potential issues
• Test the newly migrated applications and data
Week 3: Train staff on new systems
• Conduct training for staff on new systems
• Assess staff’s understanding of new systems and resolve any issues
• Provide ongoing support to staff during transition period
Week 4: Implement security measures
• Implement security measures to ensure data privacy and integrity
• Monitor system performance and identify potential vulnerabilities
• Resolve any security issues
Week 5: Finalize migration
• Finalize data and application migration
• Ensure that all systems are working properly and securely
• Perform a full system audit to ensure all data is secure
• Finalize documentation and provide wrap up report to client
Most popular offerings
Contact
Ready to meet the only technology partner you'll ever need?